6.7 KiB
| title | description | summary | date | draft | author | tags | canonicalURL | showToc | TocOpen | TocSide | weight | hidemeta | comments | disableHLJS | disableShare | hideSummary | searchHidden | ShowReadingTime | ShowBreadCrumbs | ShowPostNavLinks | ShowWordCount | ShowRssButtonInSectionTermList | cover | |||||||||||||||||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| [GSP322] Build and Secure Networks in Google Cloud: Challenge Lab | Build and Secure Networks in Google Cloud | 2023-05-26T01:08:03+07:00 | false | Hiiruki |
|
true | false | right | 10 | false | false | true | true | false | false | true | true | true | true | true |
|
GSP322
- Time: 1 hour
- Difficulty: Advanced
- Price: 7 Credits
Lab: GSP322
Quest: Build and Secure Networks in Google Cloud
Setup
Define the environment variables:
export IAP_NETWORK_TAG=
export INTERNAL_NETWORK_TAG=
export HTTP_NETWORK_TAG=
export ZONE=
Fill the variables with the values from the lab
For the zone you can check first. In the console, click the Navigation menu > Compute Engine > VM Instance. In my case I used us-east1-b
To list all available zones:
gcloud compute zones list
Reference: gcloud compute zones list
For example in my case:
export IAP_NETWORK_TAG=allow-ssh-iap-ingress-ql-901
export INTERNAL_NETWORK_TAG=allow-ssh-internal-ingress-ql-803
export HTTP_NETWORK_TAG=allow-http-ingress-ql-982
export ZONE=us-east1-b
Challenge scenario
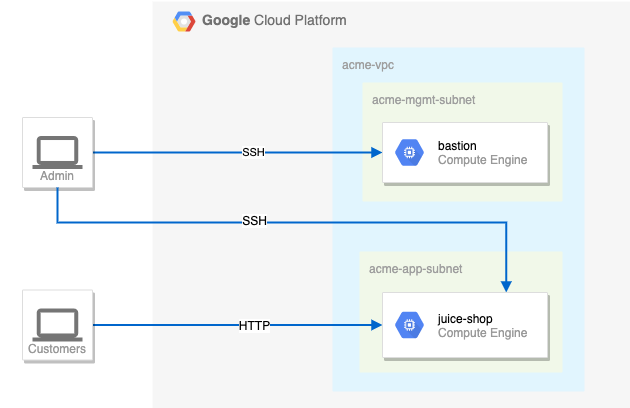
You are a security consultant brought in by Jeff, who owns a small local company, to help him with his very successful website (juiceshop). Jeff is new to Google Cloud and had his neighbour's son set up the initial site. The neighbour's son has since had to leave for college, but before leaving, he made sure the site was running.
You need to help out Jeff and perform appropriate configuration for security. Below is the current situation:
Your challenge
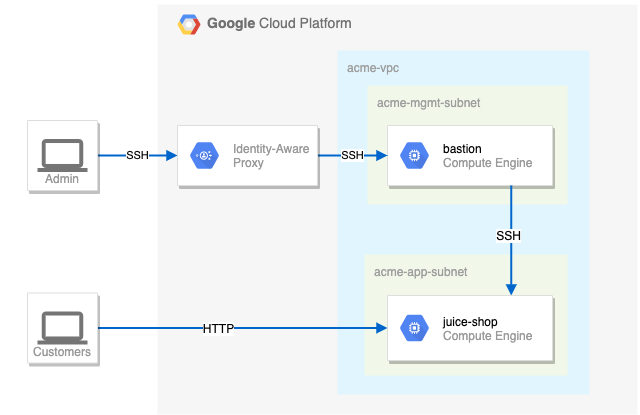
You need to configure this simple environment securely. Your first challenge is to set up appropriate firewall rules and virtual machine tags. You also need to ensure that SSH is only available to the bastion via IAP.
For the firewall rules, make sure:
- The bastion host does not have a public IP address.
- You can only SSH to the bastion and only via IAP.
- You can only SSH to juice-shop via the bastion.
- Only HTTP is open to the world for
juice-shop.
Tips and tricks:
- Pay close attention to the network tags and the associated VPC firewall rules.
- Be specific and limit the size of the VPC firewall rule source ranges.
- Overly permissive permissions will not be marked correct.
Suggested order of actions:
-
Check the firewall rules. Remove the overly permissive rules.
gcloud compute firewall-rules delete open-accessPress
yandenterto confirm. -
Navigate to Compute Engine in the Cloud Console (Navigation menu > Compute Engine > VM Instance) and identify the bastion host. The instance should be stopped. Start the instance.
gcloud compute instances start bastion --zone=$ZONEIf you getting error when run this command, you can manually activate bastion in VM Instance.
-
The bastion host is the one machine authorized to receive external SSH traffic. Create a firewall rule that allows SSH (tcp/22) from the IAP service. The firewall rule must be enabled for the bastion host instance using a network tag of
SSH_IAP_NETWORK_TAG.gcloud compute firewall-rules create ssh-ingress --allow=tcp:22 --source-ranges 35.235.240.0/20 --target-tags $IAP_NETWORK_TAG --network acme-vpc gcloud compute instances add-tags bastion --tags=$IAP_NETWORK_TAG --zone=$ZONE -
The
juice-shopserver serves HTTP traffic. Create a firewall rule that allows traffic on HTTP (tcp/80) to any address. The firewall rule must be enabled for the juice-shop instance using a network tag ofHTTP_NETWORK_TAG.gcloud compute firewall-rules create http-ingress --allow=tcp:80 --source-ranges 0.0.0.0/0 --target-tags $HTTP_NETWORK_TAG --network acme-vpc gcloud compute instances add-tags juice-shop --tags=$HTTP_NETWORK_TAG --zone=$ZONE -
You need to connect to
juice-shopfrom the bastion using SSH. Create a firewall rule that allows traffic on SSH (tcp/22) fromacme-mgmt-subnetnetwork address. The firewall rule must be enabled for thejuice-shopinstance using a network tag ofSSH_INTERNAL_NETWORK_TAG.gcloud compute firewall-rules create internal-ssh-ingress --allow=tcp:22 --source-ranges 192.168.10.0/24 --target-tags $INTERNAL_NETWORK_TAG --network acme-vpc gcloud compute instances add-tags juice-shop --tags=$INTERNAL_NETWORK_TAG --zone=$ZONE -
In the Compute Engine instances page, click the SSH button for the bastion host.
Once connected, SSH to
juice-shop.gcloud compute ssh juice-shop --internal-ipWhen prompted
Do you want to continue (Y/n)?, pressyandenter.Then create a phrase key for the
juice-shopinstance. You can just pressenterfor the empty passphrase.When prompted
Did you mean zone [us-east1-b] for instance: [juice-shop] (Y/n)?, pressyandenter.